Introduction
Building a secure, scalable, and compliant cloud foundation is the first priority for any organization migrating to AWS. A well designed AWS Landing Zone ensures that every workload operates within a governed, automated, and secure environment right from day one.
With services like AWS Control Tower, Landing Zone Accelerator, and modern AWS security best practices, cloud teams can confidently deploy a multi account AWS setup backed by enterprise grade governance and identity controls.
Whether you’re starting your AWS cloud migration or modernizing existing workloads, implementing a strong landing zone architecture is essential for long term cloud success.
In 2025, with increasing cyber threats and compliance requirements, every organization needs a well-designed, secure AWS landing zone to ensure long term success.
What Is an AWS Landing Zone?
An AWS Landing Zone is a pre-configured multi account AWS setup built using AWS security best practices and AWS governance guidelines.
It gives you:
- Centralized identity management
- Standardized network architecture
- Security controls and monitoring
- Automated account creation
- Compliance enforcement
- Guardrails using AWS Control Tower
Many organizations also use the Landing Zone Accelerator to automate deployment using best practices and Infrastructure as Code (IaC).
Why a Secure Landing Zone Matters
A secure AWS Landing Zone ensures your environment is built with:
- Strong identity controls using AWS IAM best practices
- Enforced governance across accounts
- Network isolation and segmentation
- Centralized logging and threat detection
- Compliance with frameworks like CIS, SOC2, ISO
Without proper AWS governance, organizations face misconfigurations, security gaps, and operational risk.
How to Build a Secure Landing Zone in AWS
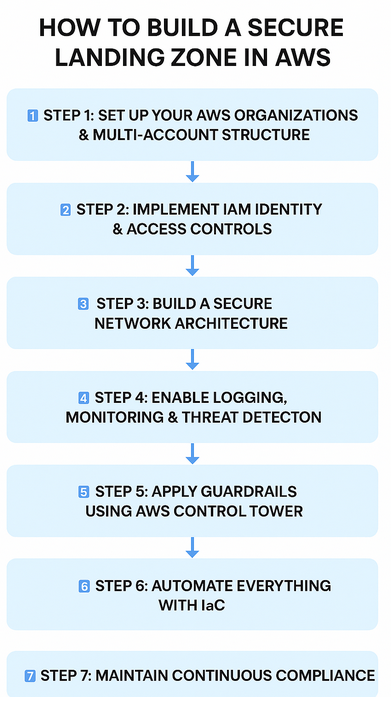
Step 1: Set Up Your AWS Organizations & Multi-Account Structure
A secure landing zone begins with AWS Organizations.
Create Organizational Units (OUs) such as:
- Security OU
- Infrastructure OU
- Sandbox OU
- Production OU
This multi account AWS setup helps isolate workloads, enforce guardrails, and maintain compliance.
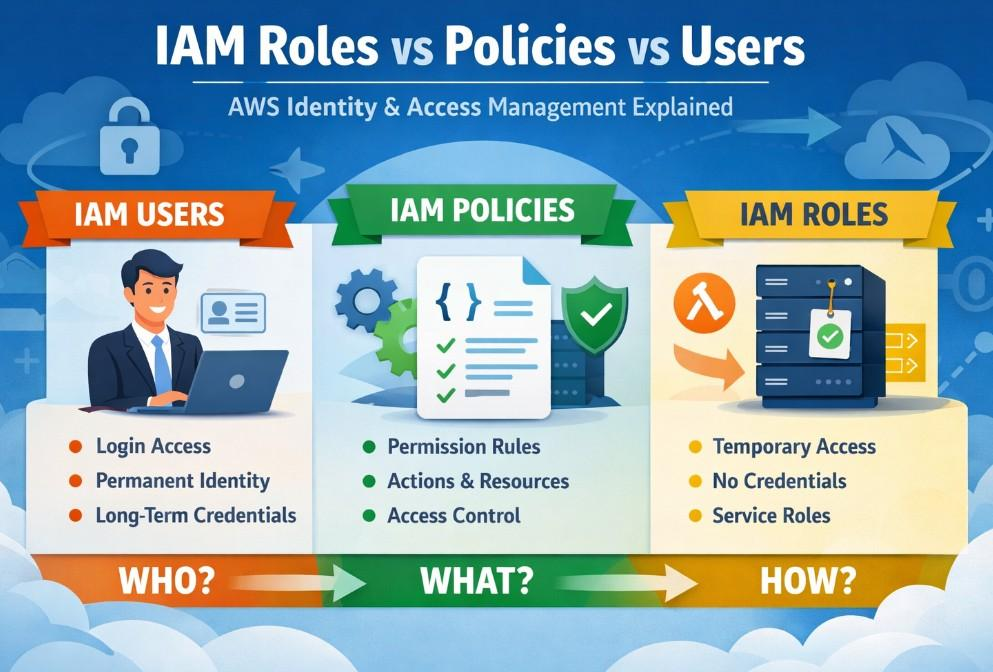
Step 2: Implement IAM Identity & Access Controls
Identity is the core of secure AWS architecture.
Follow AWS IAM best practices:
- Use IAM Identity Center (SSO)
- Enable MFA everywhere
- Apply least privilege roles
- Avoid long-term access keys
- Integrate with AD / Okta if needed
This ensures strong, centralized access governance across your landing zone.
Step 3: Build a Secure Network Architecture
A well-designed AWS network should include:
- Private subnets for workloads
- Centralized NAT Gateways
- Isolated VPCs for sensitive workloads
- Transit Gateway for scalable networking
- Route 53 for internal DNS
These network foundations ensure a secure AWS landing zone and reduce exposure.
Step 4: Enable Logging, Monitoring & Threat Detection
A secure landing zone requires continuous visibility:
- CloudTrail for API activity
- AWS Config for compliance checks
- CloudWatch for logs & metrics
- Security Hub for posture management
- GuardDuty for threat detection
These tools are essential for cloud security consulting teams designing secure architectures.
Step 5: Apply Guardrails Using AWS Control Tower
AWS Control Tower helps enforce:
- Region restrictions
- Mandatory encryption
- Preventing public S3 buckets
- Blocking root access
- Required logging across accounts
Control Tower also uses Landing Zone Accelerator patterns to speed up secure deployment.
Step 6: Automate Everything with IaC
Use tools like:
- Terraform
- AWS CDK
- Control Tower Account Factory
- Landing Zone Accelerator
Automation ensures consistent, repeatable deployments aligned with AWS security best practices.
Step 7: Maintain Continuous Compliance
Use Config Rules, Security Hub, and GuardDuty findings to monitor:
- Misconfigurations
- Unencrypted resources
- Open security group ports
- Policy violations
This keeps your secure AWS architecture aligned with enterprise governance.
Best Practices for a Secure AWS Landing Zone
- Use IAM Identity Center instead of IAM users
- Enforce MFA for all users
- Encrypt all data (S3, EBS, RDS, Lambda)
- Centralize logs into a security account
- Use CI/CD + IaC for deployments
- Regularly audit IAM roles & SCPs
- Keep networking private-first
- Use AWS governance controls
Conclusion
A secure and well designed AWS Landing Zone is the foundation for successful AWS cloud migration.
By using AWS Control Tower, applying AWS security best practices, and automating deployments through Landing Zone Accelerator, organizations can ensure a scalable, compliant, and secure AWS environment from day one.
For companies needing expert guidance in designing landing zones, cloud security consulting teams play a key role in deploying the right architecture, guardrails, and operational model.
Continue your learning journey by reading our blog on Understanding IAM Roles and Policies in Google Cloud.
What’s Next ?
We’re here to support you! Should you have any questions or need assistance, don’t hesitate to get in touch with us. Contact us at info@uranuscloudsolutions.com and we’ll be happy to help. Your satisfaction is our priority!.